Top 5 Most Common HIPAA Violations
What Medical Practices Must Do After a HIPAA Breach: Prevent Fines & Stay Secure
Why a Virtual CISO Is the Right Choice for Your Small Business in Healthcare
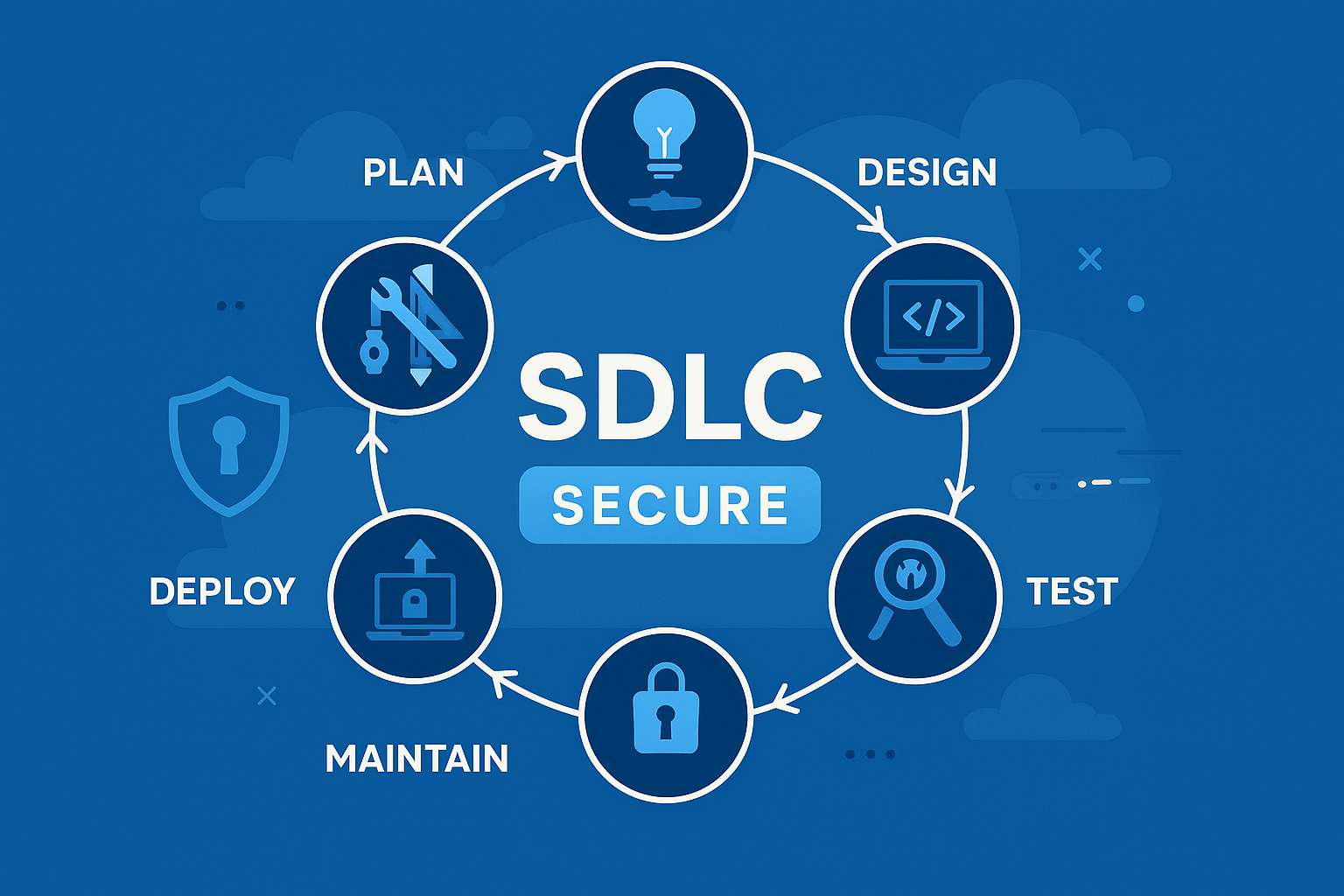
How to Build a Secure SDLC That Actually Works in 2025
Announcing Our New Virtual CISO Program
Protect Your Business from Ransomware Attacks
Best HIPAA Compliance Software for 2025: Top Solutions for Health
Ransomware-as-a-Service: The Cybercrime Business Model Fueling Attacks
Protecting Your Business in a Digital-First World – Patron Cyber Security
Easy To Use Cyber Security Platform to Protect Your Business
HIPAA Compliance Consulting in Florida
Why Every Small Business Needs a Managed Security Services Provider (MSSP)
Why Your Business Needs Penetration Testing?
Securing Your Small Business
Benefits of Red Team
Our Team That Fights Cyber Criminals
Improving your Cyber Security for Your Small Business
What Is Gray Box Testing in Application Security?
AI is helping cybersecurity companies deliver better service for their clients:
Welcome to the Patron Cyber Security Blog
At Patron Cyber Security, we believe that knowledge is the first line of defense. Our blog is dedicated to helping businesses of all sizes understand the ever-evolving cybersecurity landscape, stay ahead of emerging threats, and make informed decisions about their security posture.
Every week, we share fresh, insightful articles covering critical topics, practical tips, and real-world guidance to keep your organization secure and compliant.
Explore Our Recent Posts:
-
HIPAA Compliance Consulting in Florida
Learn why proper compliance is essential and how we help protect electronic protected health information (ePHI). -
Why Every Small Business Needs a Managed Security Services Provider (MSSP)
Discover how partnering with an MSSP can give your business 24/7 protection and peace of mind. -
Why Your Business Needs Penetration Testing
Understand the value of proactive testing to identify and close security gaps before attackers can exploit them. -
Securing Your Small Business
Get actionable tips to strengthen your security posture, even with limited resources. -
Benefits of Red Team
See how simulated attacks can uncover hidden vulnerabilities and improve your defenses.
Stay Connected
Be sure to check back every week for new articles designed to empower you with the knowledge and strategies you need to protect your data, your customers, and your reputation.